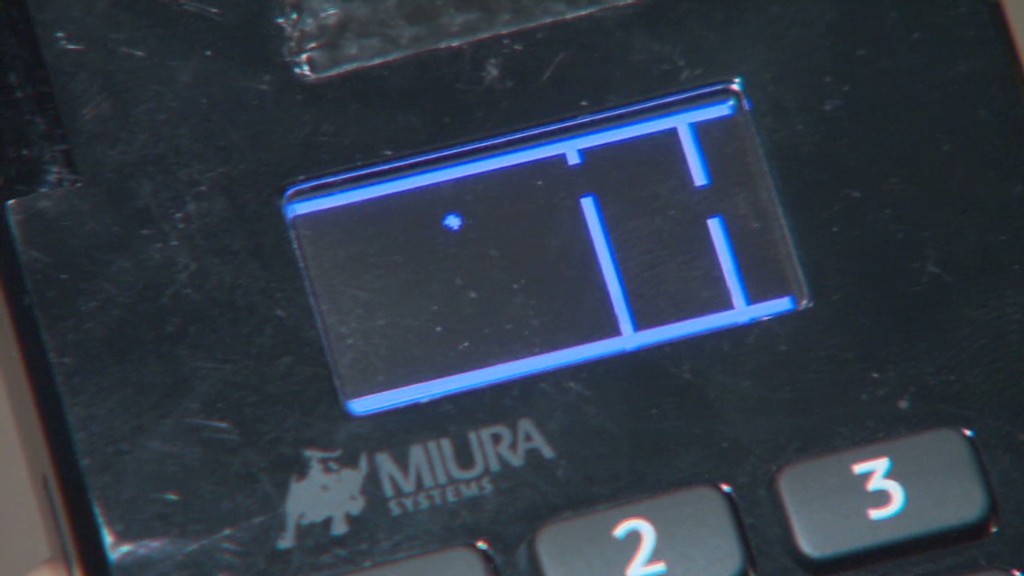
Get ready for a facepalm: 90% of credit history card visitors at the moment use the identical password.
The passcode, established by default on credit history card equipment due to the fact 1990, is quickly located with a rapid Google searach and has been exposed for so lengthy there is no sense in attempting to conceal it. It can be either 166816 or Z66816, relying on the machine.
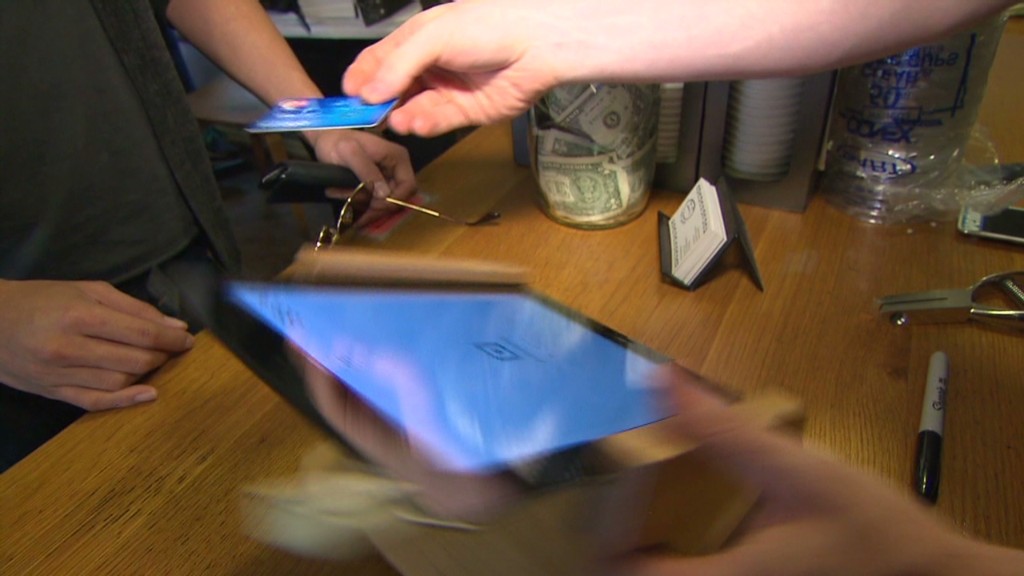
With that, an attacker can obtain complete regulate of a store’s credit rating card viewers, probably allowing them to hack into the equipment and steal customers’ payment facts (feel the Target (TGT) and House Depot (High definition) hacks all around again). No surprise major retailers keep getting rid of your credit rating card details to hackers. Safety is a joke.
This most up-to-date discovery will come from scientists at Trustwave, a cybersecurity business.
Administrative entry can be applied to infect equipment with malware that steals credit rating card info, stated Trustwave govt Charles Henderson. He specific his findings at last week’s RSA cybersecurity meeting in San Francisco at a presentation named “That Level of Sale is a PoS.”
Consider this CNN quiz — uncover out what hackers know about you
The trouble stems from a recreation of hot potato. System makers offer devices to unique distributors. These suppliers promote them to retailers. But no a single thinks it is really their career to update the learn code, Henderson told CNNMoney.
“No just one is shifting the password when they established this up for the to start with time everyone thinks the safety of their level-of-sale is someone else’s accountability,” Henderson claimed. “We’re making it pretty quick for criminals.”
Trustwave examined the credit rating card terminals at far more than 120 suppliers nationwide. That includes main apparel and electronics outlets, as effectively as regional retail chains. No specific vendors were being named.
The large bulk of equipment were designed by Verifone (Pay back). But the similar concern is present for all key terminal makers, Trustwave claimed.

A spokesman for Verifone explained that a password by yourself is just not adequate to infect machines with malware. The company stated, right up until now, it “has not witnessed any attacks on the protection of its terminals based mostly on default passwords.”
Just in scenario, although, Verifone mentioned suppliers are “strongly encouraged to alter the default password.” And currently, new Verifone units occur with a password that expires.
In any circumstance, the fault lies with suppliers and their specific suppliers. It really is like property Wi-Fi. If you obtain a residence Wi-Fi router, it is up to you to improve the default passcode. Retailers ought to be securing their very own machines. And machine resellers ought to be serving to them do it.
Trustwave, which can help defend shops from hackers, mentioned that keeping credit history card devices protected is small on a store’s checklist of priorities.
“Firms expend extra revenue selecting the shade of the point-of-sale than securing it,” Henderson explained.
This problem reinforces the conclusion built in a latest Verizon cybersecurity report: that stores get hacked due to the fact they’re lazy.
The default password detail is a serious problem. Retail computer networks get uncovered to personal computer viruses all the time. Take into account 1 circumstance Henderson investigated a short while ago. A horrible keystroke-logging spy program ended up on the personal computer a retailer utilizes to process credit score card transactions. It turns out employees had rigged it to engage in a pirated edition of Guitar Hero, and unintentionally downloaded the malware.
“It exhibits you the level of access that a good deal of people today have to the stage-of-sale surroundings,” he explained. “Frankly, it can be not as locked down as it need to be.”
CNNMoney (San Francisco) To start with printed April 29, 2015: 9:07 AM ET






More Stories
Pagaya share price begins to lose ground
In a sea of bad news, here are our 10 top tales to make you smile
Shekel staged strong comeback in July